Security researchers have discovered bad news for WiFi wireless networks everywhere. Several key control vulnerabilities within the four-way handshake of the WPA2 security protocol, which helps preserve present-day Wireless Local Area Networks (WLAN) relaxed through encryption, were observed. Hopefully, now, anybody has ensured that their home wi-fi community and devices are all linked to the usage of the ultra-modern Wi-Fi Protected Access II (WPA2) approach of encryption, which has to date served us all well. The bad news is that a string of recent vulnerabilities was discovered that could result in WPA2-secured networks being decrypted, hijacked, and generally abused (it works against each WPA1 and WPA2 – private and company networks – and in opposition to any cipher suite getting used like WPA-TKIP, AES-CCMP, and GCMP).
As the USA Computer Emergency Readiness Team (US-CERT) states, “The impact of exploiting these vulnerabilities includes decryption, packet replay, TCP connection hijacking, HTTP content injection, and others. Note that as protocol-stage problems, most or all correct implementations of the standard might be affected.” The info of all this is because of being published quickly through numerous vulnerability announcements (CVE-2017-13077, 13078, 13079, 13080, 13081, 13082, 13084, 13086, 13087, 13088), and the collection of flaws are being referred to as KRACK (aka – Key Reinstallation Attacks). A committed internet site has even been set up through the researchers to offer information at the incoming hassle.
We discovered critical weaknesses in WPA2.
A protocol that secures all cutting-edge covered Wi-Fi networks. An attacker within range of a sufferer can make the most of these weaknesses using key reinstallation assaults (KRACKs). Concretely, attackers can use this novel assault technique to read records that were formerly assumed to be safely encrypted. This may be abused to steal touchy records such as credit score card numbers, passwords, chat messages, emails, images, and so forth. The assault works towards all modern included Wi-Fi networks. Depending on the network configuration, it is also viable to inject and manage records. For instance, an attacker is probably capable of injecting ransomware or different malware into websites. The weaknesses are inside the Wi-Fi fashionable itself, and now not in-person products or implementations. Therefore, any correct implementation of WPA2 is probably affected.
I Had a Panic Attack!
For those who understand me, you realize I use humor in each aspect of my life. From the scientific paintings, I do with my clients to how I relate to friends and family. Always have, always will. It virtually enables me with my paintings as a trauma-informed therapist, specializing in Domestic Violence and all the emotional leftovers that include: tension/panic, PTSD, despair, codependency, anger, low self-esteem, etc. So I looked to take my comedic hobby to the next stage and do something positive about it. So I signed up for improv training at The Second City in Chicago.
Read More Article :
- Google and Rep. David Cicilline Host Internet Safety Event
- Tips to Prevent Phishing Attacks
- An In-depth Understanding of the Types of Satire With Examples
- The playlist: digital – Jlin, Oneohtrix Point Never, Acre, and more
- 8 Vital Signs That Tell You Are Overpaying for Your Auto Insurance
And then I had a panic assault!
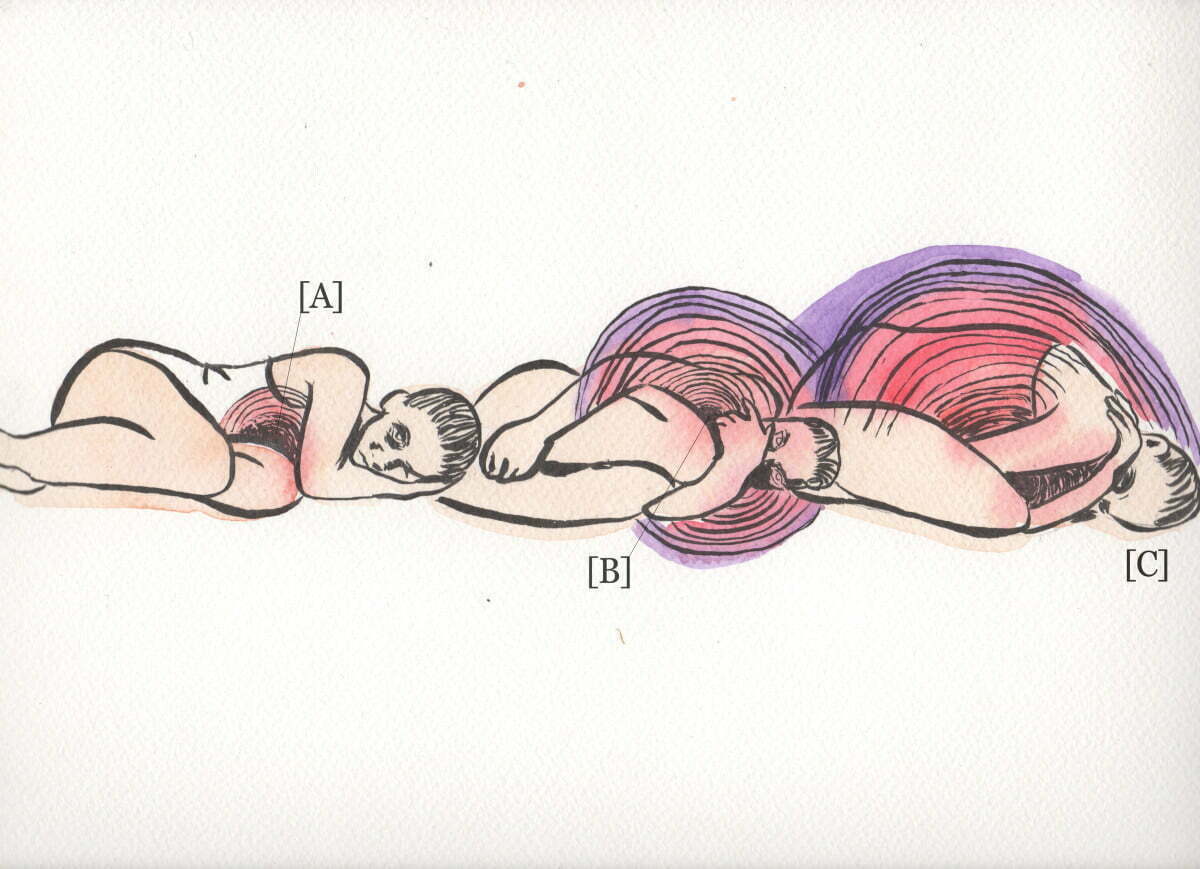
I recognize what a panic attack is. I help customers day in and time out apprehend how anxiety works inside the frame and how panic attacks manifest. When we perceive a chance, our frame reacts. We cross into combat, flight, or freeze. This becomes useful whilst our caveman ancestors tried to run or shield themselves towards an attack from a saber teeth tiger. It allowed our body to respond the way it ought to, with a boost in norepinephrine (an organic chemical that acts as a hormone and neurotransmitter). It tells our mind we are in chance and activates our frame’s fight or flight reaction. Our frame became designed to cope with the threat, handle it, and move on. When we are constantly flooded with norepinephrine, we can stimulate our combat or flight response too regularly, mainly to panic assaults. The Mayo Clinic defines panic attacks as a sudden onset of worry that triggers severe bodily reactions when there, in reality, isn’t any cause. Many people enjoy them at the grocery save, at their children’s soccer sport, in elegance, or while sitting out at home.
So once I had one, I knew precisely what it turned into. It did not make the experience any much less horrifying or uncomfortable. In reality, I ended up with a true empathic reference to what my customers revel in regularly. It turned into lousy. Debilitating. And then I had to manage it on my very own, without medication, and before work. I realized I had to comply with the commands I deliver to my customers certainly. Here’s what I did…
Acknowledge you have a panic assault.
Just well known. Don’t choose it. Could you not create a tale around it? Acknowledge it right here and now and realize that it will reach the top within 10 minutes and typically subside after 20-30 minutes. This does not do plenty for the panic assault. But at least you understand it’s no longer going to kill you. Breathe. Place one hand on your chest and one hand on your belly. Inhale through the nostril, and push your stomach out – you ought to feel the hand in your stomach rise. Exhale slowly and sense your stomach decreases. If the hand on your chest is transferring, you are shallow respiratory. That simplest activates the frame’s combat or flight reaction and runs the chance of getting every other panic attack after this one dissipates.
The Impact of the Internet on Contemporary Literature
Literature is the whole lot that has ever been written. Anything from the earliest poems of Homer to modern internet pages may be considered literature. But for a selected feel, there are numerous varieties of literature. Literature may be written in a selected language, like English Literature, or be written using a particular subculture, including African Literature. But literature clearly method greater than printed phrases, and the internet, in reality, is a part of literature. I must be aware that the phrase literature comes from the French word belles-lettres, which means “stunning writing.” When a bit of work is referred to as literature, it is usually considered an exquisite painting of art. The net literature does not necessarily need to be in this manner because nobody controls the net literature. In the following essay, I will talk approximately the impact of the internet on the literature nowadays.
There are two predominant training of literature which is additionally present on the internet: fiction and nonfiction. Fiction is writing that a creator creates from the imagination. Authors might also include non-public revelations or facts about actual people or events. However, they combine those statistics with imagined situations (Moran, forty-five). In non-net literature, the mission undergoes as a minimum some censorship in phrases of what words may be used, but the internet lets the authors put something they desire on the website and enjoy it. Most fiction is narrative writing, which includes novels and quick testimonies. Fiction also includes drama and poetry. Nonfiction is real writing approximately actual-existence conditions. Nonfiction’s essential styles include the essay, biography, autobiography, and diary (Browner, ninety). The internet gives brand new paperwork–net pages or netbooks.
People study literature for a diffusion of motives.
The most unusual cause for analysis is satisfaction. People study to skip the time or for facts and understanding. Through literature, humans meet characters they could discover and then discover answers to their troubles. With literature, someone can often understand conditions they could not in any other case recognize in actual lifestyles (Koehler, 28). Often, just the phrases’ association can be exciting, simply as a toddler likes the sound of “Ring Around the Rosie,” even though they won’t apprehend what the phrases mean. There are four factors of literature: characters, plot, subject matter, and fashion. A precise author can stabilize these elements, creating a unified painting of artwork.
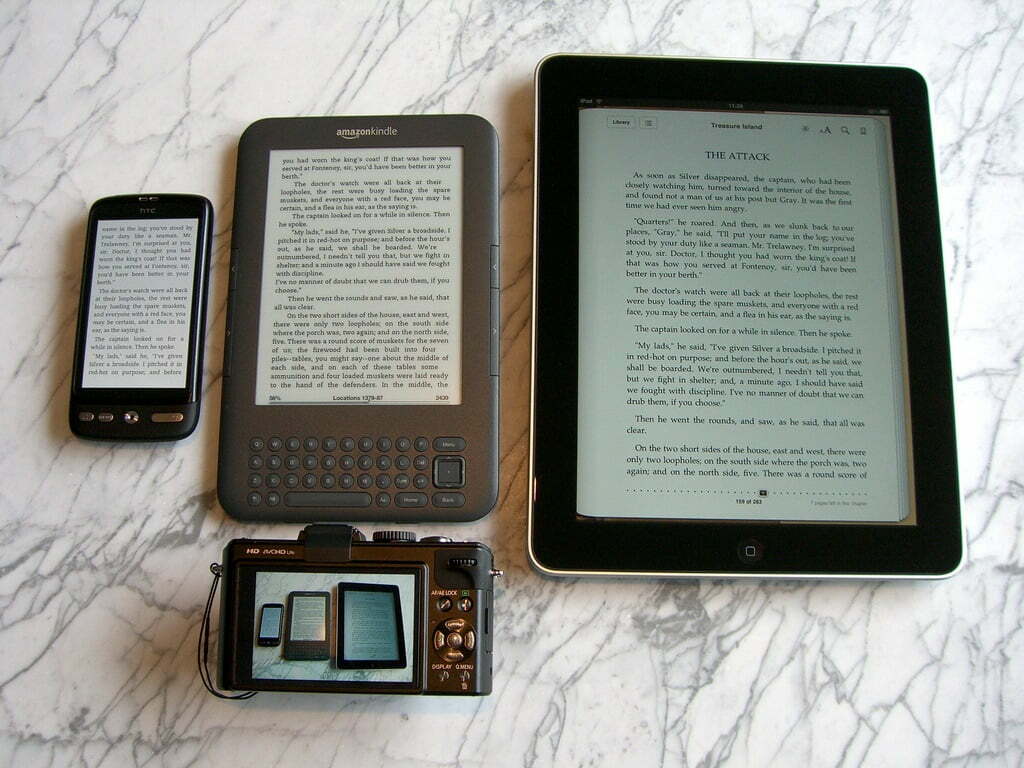
The characters make up the significant interest of many dramas and novels biographies and autobiographies. A creator must recognize each individual thoroughly and have a clear idea about everyone’s appearance, speech, and thoughts. Internet literature isn’t hard to create for the reality that not like “traditional” literature, the net literature calls for minimum begin-up fees (Moran, forty-seven). And because reading normally includes comfort, at some point in time, one could no longer be amazed to look at convenient digital devices that could be transported anywhere and download books from the internet and gift them in a virtual format.
Role of Safety Barriers in Perimeter Security

To guard employees, guests, and the building functions and offerings from any disturbances together with unauthorized motors coming near or entering excessive risk constructing, Perimeter protection is followed. Depending on the building’s cost and the dimensions of the chance, safety is finished with the aid of setting up a suitable standoff distance. This is possible with the use of a safety barrier machine to provide the necessary standoff. The barriers may be along with the website online of the assets line, within a huge campus or web page, placed separately from the property line. The barrier can shape an interface between the public and the personal space alongside the property line.
A perimeter protection system consists of primary elements,
- – An inflexible barrier consisting of a concrete barrier that prevents unauthorized pedestrians or cars from entering the region
- – A control factor that could screen and look at everyone earlier than they skip via the barrier
Some blessings of having safety limitations for the safety of a public area are listed under,
- In any public area, it is vital to have perimeter safety to protect the construction and its occupants and preserve the presence and activity of the public. Having protection barriers can provide a precise balance between them.
- – Barriers are to be had in diverse shapes and sizes. By choosing the proper obstacles, the aesthetic cost of the location is stepped forward. It offers protection in the context of enhancing the specific spot and the location around it instead of as a separate or redundant machine whose handiest cause is to provide security.
- – This barrier system affords a unique course to the upcoming vehicles, and the access is screened in an orderly way, allowing one car at a time. The ultimate aspect of the safety of the constructing desires is to have a pile-up earlier than the gate.
- – It provides the perfect vicinity separation carrier for cars. Barricades can divide various elements of any place, especially the indoors, to get the right of entry to everybody apart from the building’s employees. Therefore, the personnel can avoid any dilemma by blending up with the site visitors.
- – It also can be made to form a pathway to the ticket counter or some other services.
- – It can provide extra protection to the assets of the construction.
- – It is a great manner to guide automobiles inside the parking lot and to disclaim get admission to areas that might be reserved for any important personnel.
- – It can keep away from any unintended entry of visitors to any “No-Go” zones. Visitors aren’t usually alert enough to be aware of any caution signs close to the door.

