Developed first at the AT&T laboratories, Unix is now in the hands of various earnings corporations. This article presents a listing of simple Unix instructions.
TAGGED UNDER: Computer Operating Systems
If you need to learn how a working system works, getting to know Unix is perhaps the best way. To understand this device, you must have a listing of primary Unix instructions. This article will provide you with the identical, and you may apprehend the purpose of every command. You will also apprehend why it’s far necessary to recognize them thoroughly. They assist us in interacting with the PC when using this operating system. Likewise, this list is the same as the one used for Linux, unlike Unix.
Basics
An operating device is an interface between the user and the laptop. The Unix-running gadget is designed to augment the same purpose. However, the technique changed to open supply software. It is a gadget software, and the person may manage all of the strategies inside the operating device. The middle of this system is called the kernel. The kernel is liable for coping with all of the inner operations of the working gadget. From allocating hardware to multi-consumer and multitasking centers, the duties are achieved for the kernel. This running system gives you centers proper from loading decided-on applications for a particular consultation to terminating and resuming methods at will. There are commands to deal with almost every operation.
Read More Article :
- Spurred using Marcel News, R/GA Announces Its Own ‘Operating System.‘
- List of Mac Equivalents to Windows Software Programs
- Apstra Operating System gets Layer 2 records middle community guide
- Building a comfy working device with Roger R. Schell
It is used to list the files and directories in any listing. It would help if you had to look at the prompt and get all the files and folders in that precise directory. There are diverse switches, too, which could help list the names of those files and directories. For instance, in case you kind is a, you could get the listing of the hidden documents in conjunction with the alternative files indexed. Hidden record names begin with a (.) dot.
Mkdir
It is used for growing directories. For instance, if you kind media ABC, the listing ABC can be created inside the present-day listing.
Cd
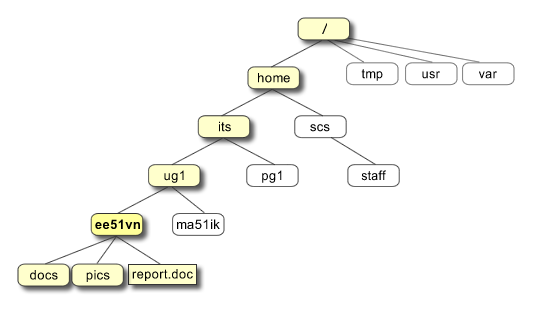
This is used to change from one directory to another. If you are working within the listing ABC and you need to trade to the directory CBA, you want to type CBA. In this case, the directory CBA should be inside the ABC. If the listing CBA is absent within the listing ABC, you cannot circulate it to that directory. You’ve got to say the whole route location to the listing CBA starting from the base directory under such instances. Suppose the directory CBA is present in the directory def beneath the root(/) listing; then you need to kind, cd /dev/CBA, to transport over to that directory. If you want to transport over to the figure listing of ABC, which is to say puzzle, you need to type cd.
PWD
If you have reached a listing through various directories and are not privy to the route to the directory, you could, without a doubt, use Kitypen PWD to get the current area path. Suppose you’re in the listing him. Hij becomes think created in the listing def, under the listing ABC created beneath the foundation. Then, when typing PWD, you get is/ABC/def/hit.
Copying, Moving, and Deleting
Suppose you want to duplicate the file inventory.Txt in your modern directory. In such cases, the cp can be used to make the copy. Cp /abc/inventory.Txt inventorybackup.Txt will copy the file inventory.Txt in the directory ABC created beneath the basis to your present-day operating listing and call it inventorybackup.Txt. Thus, the syntax is cp file1 file2. Here, file1 is the file name you need to replicate, and file2 will be the report’s call when it’s miles copied to the current listing. Remember, the unique record is by no means hampered in this case.
Mv
This is a multipurpose command. However, it cannot be used most effectively with the file, but you also need to transport the document stock.Txt created in the directory ABC to your modern listing; then all you want to do is mv /abc/stock.Txt… The dot (.) on the quit indicates a cutting-edge directory. When you use this, you may be left with just one file. This does not replicate the report but takes it from one area to another. Suppose we’ve got the document abc.Txt for your modern listing. When typing mv abc.Txt def.Txt, the record abc.Txt may be renamed def.Txt.
Rm
This is used to dispose of or delete a document. So, if you can rm abc.Txt, the file can be completely deleted from the gadget.
Radio
This operates much like rum. But it is used for disposing of or deleting directories. So, when typing radio ABC, you can delete the listing ABC all the time.
File Content Viewing
It can be used to develop and view the contents of a report. Suppose you need to view the contents of the document abc.Txt, then you could type cat abc.Txt. On typing this, you will get the contents of the file abc.Txt displayed on your display screen. If the report abc.Txt does not exist, then it will likely be created by typing the command.
Much less
You can see the information in a record, one page at a time. This is necessary if the file contains a lot of content. For instance, typing less abc.Txt will display the contents of the file abc.Txt, one web page at a time.
Head
This is used to show the first ten strains of any file on your display screen. If you type head abc.Txt, you will see the primary ten traces of the report abc.Txt.
Tail
It works just like ahead. But right here, the final ten traces of the document may be considered. So, typing tail abc.Txt will gift you the last ten lines of the document abc.Txt.
Using Wildcards Asterisk (*)
The asterisk signal is one of the wildcards that you could use in any Unix command. To understand the software of the wildcards, let us take an example. Suppose you need to list out all of the files that give up with the phrase ‘vintage.’ In this case, if you are kind of *antique, all documents that grow to be with the words old, like fold, gold, and many others, can be listed.
Question Mark (?)
The query mark can update just one man or woman. So, if you want to list all the filenames that give up with the word puzzle and have the most effective one starting a letter, then you can type ls. Uzzle. So, all the files containing a puzzle, like a puzzle, puzzle, etc., are found in that directory.
Others echo
This is one of the most commonly used ones. It presents the price of any variable. For instance, if a variable $printer (all variable names in Unix start with the $ signal) has the value, Cannon, then when typing echo $printer, Cannon could be displayed on the computer display screen.
Guy
You can type guy accompanied by the command name to display the guide for all commands. You will get all the facts, such as the switches you may use at the side of the command to decorate your execution further.
Whatis
When typing what is observed using the command’s name or any command, you will get the basic operating of any command.
Advanced ps
You can use this to check the list of processes and their method IDs running on your PC machine. A technique ID is a variety used for identifying techniques and is precise for every procedure.
Kill
It is used to terminate any manner in which this is being performed. It is just like the ‘end task’ that we use in Windows. Here, we must use kill accompanied by the manner identity or PID, i.e., kill PID. For instance, if we want to kill the procedure cat with a PID of 1134, we will kill 1134 in our set.
Chmod
This is one of the most crucial commands used for file security. For expertise, its use allows us to attempt to gauge some alternatives that it gives. The precedence and rights of a record rely upon the three fundamental kinds of users—the owner user (u), the institution(g), and the other(o). Permissions to read, write, and execute are given to each consumer. The execute permission is represented by #1, the write through the range 2, and the study using four. Now, think the person or the proprietor of the report, ABC, has all three permissiothrees; he could have total permission wide variety of 7 (four+2+1). If the group users have just examined permission, their total permission quantity will be 4 (4+zero+0). Suppose the opposite users only have permission to execute the record; they may have total permission of 1 (zero+0+1). So, the permission associated with the document will be 741. Changing this permission will change the person’s rights to the record. So, within the same instance, if we need to change the permission of the consumer to examine and write and the group and different consumer to execute, we will execute the command as Richmond ABC 611. The different way is that you may take away the consumer’s execution rights by typing mod ABC u-x. To add study and writing permission for the organization and other users, you may find the kind mod ABC pass+rw. Remember, the handiest file owner has the right to use the mod command in the report.
All the Unix instructions defined above have a list of options or switches used in conjunction with them. There are many extra instructions, which you could use and look at when you pass for an in-intensity study of this top-notch working system. The abovementioned ones will help you research the OS and use it more efficiently. Truly using them, you can not analyze Unix best but can comprehend the fundamentals of working structures. All the one-of-a-kind operating structures are primarily based on the same fundamental standards as Unix.

